“The important thing about outsourcing or global sourcing is that it becomes a very powerful tool to leverage talent, improve productivity, and reduce work cycles.” — Azim Premji, Chairman of Wipro Limited.
While Mr. Premji’s sentiment holds true, outsourcing is a double-edged sword. For every company that scales successfully using global talent, another faces setbacks due to poor planning, communication breakdowns, or security lapses.
A few days ago, a close associate in the industry approached me. He was eager to find an outsourcing partner to scale his operations but was paralyzed by the horror stories he’d heard. He knew outsourcing wasn’t risk-free. His priority wasn’t just finding a vendor; it was finding a safe way to work with one.
That conversation sparked this guide. If you are looking to leverage global talent but are worried about the potential pitfalls, you are in the right place.
Below, we dissect the current landscape of the outsourcing market and provide a deep dive into the top 13 outsourcing risks—and, most importantly, the specific strategies to mitigate them.
Outsourcing Market: The Context
Before analyzing the risks, it is vital to understand the magnitude of the industry. Outsourcing is no longer a niche tactic; it is a global economic pillar.
Predictions for the sector have consistently pointed toward massive growth. Historical data from 2021 projected IT outsourcing revenue to top $359 billion, with spending per employee reaching over $104. Estimates suggested the market would surge by nearly $98 billion between 2020 and 2026, growing at a CAGR of 5%.
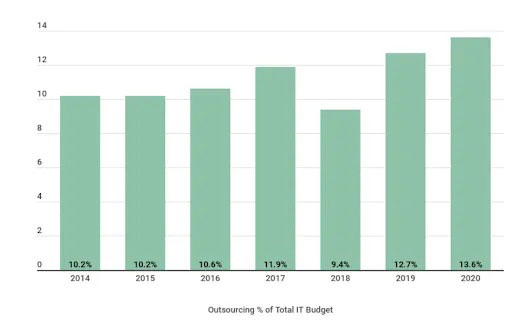
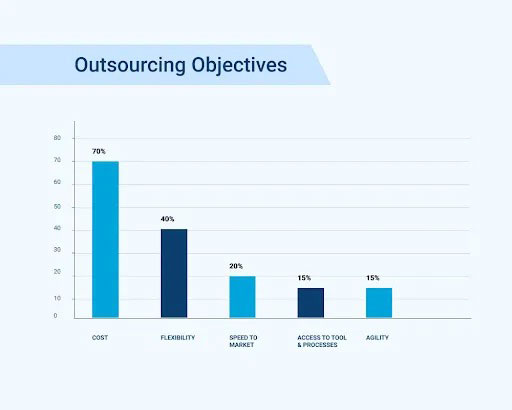
However, the landscape has shifted. According to Deloitte’s Global Outsourcing Survey, the focus has moved beyond just cost-cutting. Businesses are now prioritizing resilience, agility, and access to specialized technology stacks. But as the market grows, so does the complexity of managing these relationships.
13 Top Outsourcing Risks and Their Solutions
The most effective way to neutralize risk is preparation. Whether you are hiring a software development company in India, Eastern Europe, or Latin America, the challenges remain largely the same. Here is how to tackle them head-on.
Risk 1: The Trust Deficit
Trust is the currency of any business relationship. When you send proprietary data or core business logic to a third-party partner—whether they are domestic or international—you are taking a leap of faith. A lack of trust can paralyze decision-making and lead to micromanagement, which defeats the purpose of outsourcing.
The Mitigation Strategy:
- Start with Security Tools: Use enterprise-grade security tools. Solutions like ExpressVPN can safeguard data transmission, ensuring that your connection to remote teams remains encrypted and invisible to prying eyes.
- The “Small Win” Approach: Do not hand over the keys to the kingdom on day one. Start with a pilot project to test the waters.
- Contractual Trust: Trust should be legally binding. A solid contract must outline exactly what data is shared, how it is used, and the penalties for misuse.
- Face-to-Face Interaction: Regular video meetings (Zoom, Google Meet) build rapport. It is harder to mistrust someone when you interact with them regularly and see their working environment.
Risk 2: The Boundary of Responsibility
Outsourcing vendors often split teams into different units to maximize efficiency. However, this can lead to fragmented responsibility. If it is unclear who is responsible for a specific module or security protocol, vulnerabilities emerge. You do not want a scenario where a remote staff member has unrestricted access to your entire company database simply because roles weren’t defined.
The Mitigation Strategy:
- Principle of Least Privilege: Make it clear that your proprietary information stays within your walls. Share only what is strictly needed for the smooth delivery of the current sprint.
- Segregated Environments: Ensure your vendor uses development environments that are separate from your production data. They should build the car, not drive it with your customers inside.
Risk 3: Lack of Transparency in Tech Stacks
Some outsourcing agencies are secretive about their internal processes or the specific technology stacks they use. They might do this to prevent clients from poaching their developers or to hide the fact that they are using outdated legacy systems. This “black box” approach prevents you from knowing if your product is being built on a future-proof foundation.
The Mitigation Strategy:
- Technical Discovery: During the initial talks, demand transparency. Ask specific questions: What frameworks are you using? How do you handle version control? Can we see your deployment pipeline?
- Code Reviews: Insist on the right to perform independent code reviews. If they refuse to share the “recipe,” do not buy the meal.
Risk 4: Misaligned Business Priorities
An outsourcing partner aims to solve your problem, but they often view “success” differently than you do. You might prioritize speed-to-market, while they prioritize perfect code structure (or vice versa). If you aren’t clear, an inexperienced vendor might spend weeks polishing a feature that isn’t critical to your MVP, wasting budget on low-priority items.
The Mitigation Strategy:
- Agile Reporting: Hire a partner that adheres to Agile methodologies. They should report work after every development cycle (sprint).
- Real-Time Visualization: Use project management tools to track progress in real-time. Do not rely on weekly emails.
- Visual Documentation: Requirement documents should include screenshots, wireframes, and diagrams. Everyday business language often fails to convey technical nuance; visuals ensure everyone is literally “seeing” the same goal.
Risk 5: Intellectual Property & NDA Breaches
This is the nightmare scenario: You hire a firm to build a revolutionary app, and six months later, a competitor launches a strangely similar product. Vendors often work with multiple clients in the same niche. Without protection, your trade secrets are at risk.
The Mitigation Strategy:
- Ironclad NDAs: Never share a single byte of data before a Non-Disclosure Agreement (NDA) is signed.
- Specific Terms: The NDA must be comprehensive. It should cover:
- Strict limits on confidentiality.
- Responsibilities of both parties.
- Severe penalties for breaches.
- Non-compete clauses preventing the vendor from working with direct competitors for a set period.
Risk 6: Data Handling and Security Architecture
Transparency is crucial, but security architecture is non-negotiable. You need to know exactly how your data moves through the vendor’s network. Is it stored on local laptops? Is it on a shared server? If their network is breached, your business is compromised.
The Mitigation Strategy:
- Detailed Security Audit: Demand to know their security protocols.
- Access Control: Who has admin rights?
- Network Isolation: Client information should be kept in an isolated network segment.
- Authentication: Robust multi-factor authentication (MFA) must be mandatory for all their employees accessing your system.
- Shared Defense: The security measures protecting the outsourcer’s network must be compatible with yours.
Risk 7: The “Ghosting” Effect (Tracking Progress)
If you are outsourcing website maintenance or long-term development, you risk paying for hours that weren’t actually worked. Inaccurate reporting or “padding” hours is a common fear. You don’t want to pay for a service you aren’t receiving.
The Mitigation Strategy:
- Mandatory Tool Integration: Do not accept manual timesheets. Grant the vendor access to your Project Management (PM) ecosystem (Jira, Trello, Asana).
- Granular Tracking: You should be able to see who is working on what task and how much time has been logged against it.
- VPN Access: Top-tier outsourcing companies often allow you to access their development servers via VPN to verify work-in-progress code directly.
Risk 8: Lack of Flexibility
Business needs change rapidly. You might need to pivot your strategy halfway through a project. A rigid outsourcing partner that has been delivering the same “cookie-cutter” service for years may be unable (or unwilling) to adapt to these changes without charging exorbitant change fees.
The Mitigation Strategy:
- Scenario Testing: During the interview process, ask “What if?” questions. What happens if we need to change the tech stack in month two? What if we need to scale the team down for a month?
- Flexible Models: Look for vendors offering Time & Material (T&M) models rather than just Fixed Price contracts. T&M allows for greater agility as requirements evolve.
Risk 9: The Knowledge Gap
You hire an agency because they claim to be experts. The risk is discovering mid-project that they lack the specific expertise or “domain knowledge” required for your vertical (e.g., Fintech, Healthcare compliance).
The Mitigation Strategy:
- Verify, Don’t Trust: Assess their expertise deeply.
- Reference Checks: Ask for references specifically from past clients in your industry.
- Team Interviews: Don’t just talk to the sales rep. Interview the actual lead developer or project manager who will handle your account. Ask about the specific tools and libraries they intend to use.
Risk 10: Reliability and Stability
A vendor might be talented, but are they stable? Small, fly-by-night agencies might face cash flow issues, staff turnover, or infrastructure failures. You cannot afford for your development team to disappear overnight.
The Mitigation Strategy:
- Go Multinational: Whenever possible, choose companies with a global footprint or at least established offices in major tech hubs.
- Redundancy: Companies with offices in different countries (or well-distributed remote teams) offer better disaster recovery. If one office faces a power outage or lockdown, the other locations can pick up the slack.
Risk 11: Communication Breakdowns & Scope Creep
Poor communication leads to “Scope Creep”—where the project slowly grows beyond the original agreement, blowing the budget and deadline. If the vendor cannot meet deadlines or fails to flag issues early, it can cost you your business.
The Mitigation Strategy:
- Define Communication Policies: Set the rules before the kickoff. How often do we meet? What is the escalation path?
- Scheduled Touchpoints: Do not rely on “milestone reporting” alone. Implement daily or weekly stand-ups.
- Tooling: Use tools like Slack or Microsoft Teams for quick queries, but keep formal decisions in the PM tool or email for a paper trail.
Risk 12: The “Band-Aid” Solution
Some vendors propose the easiest, fastest solution rather than the right solution. They might suggest a workaround (a band-aid) to fix a bug because it requires less effort than refactoring the code properly. This creates “technical debt” that you will have to pay for later.
The Mitigation Strategy:
- Case Studies: Ask for case studies where they solved complex architectural problems.
- Long-Term Vision: Ask them how their proposed solution scales. If they cannot explain how the system handles 10x the traffic, they are likely proposing a short-term fix.
Risk 13: Unclear Objectives (The Client’s Risk)
This risk lies with you. The vaguer you are about your requirements, the less accurate the vendor’s estimate will be. If you don’t know what you want, you can’t blame the vendor for not building it.
The Mitigation Strategy:
- The “What,” Not the “How”: Communicate your business needs and user goals clearly, but give the experts space to propose the technical “how.”
- Discovery Phase: If your objectives are fuzzy, pay for a “Discovery Phase” first. Let the vendor help you scope the project before you sign a development contract. This ensures accurate time and cost estimation.
Why Does Your Business Need Outsourcing?
Despite the risks detailed above, the strategic value of outsourcing is undeniable. As Michael Corbett, Chairman of the IAOP, noted, the real power of outsourcing is increasing an organization’s core capacity for change and growth.
Why take the risk? Because the rewards are transformative.
1. Save Time and Money
Your resources are finite. Outsourcing converts fixed costs (salaries, benefits, office space) into variable costs. You pay only for what you need, extending your runway and freeing up capital for growth.
2. Focus on Your Core Competency
We all have strengths. If you are a marketing agency, your strength is strategy, not IT maintenance. If you are a healthcare provider, your strength is patient care, not app development. Outsourcing allows you to delegate the “noise” so you can focus on the signal.
3. Access to Global Talent
Refusing to outsource limits you to the talent pool within a 20-mile radius of your office. Outsourcing opens the door to the top 1% of talent globally. It is no longer a choice but a necessity to stay competitive.
4. New Market Opportunities
Trying to tackle every challenge internally is impossible. An outsourcing provider acts as a strategic partner, allowing you to enter new markets or launch new products simultaneously without overburdening your internal team.
Conclusion
We have discussed the critical risks—from data breaches to communication gaps—and mapped out the exact strategies to avoid them. This list is your safeguard.
While new risks may emerge as technology evolves, using this guide as your framework will keep the majority of threats at bay. Outsourcing is not about losing control; it is about extending your capabilities.
Are you ready to scale? Do not let fear hold you back. With the right due diligence and a trusted partner, you can turn these risks into your competitive advantage.
Ready to Build Your Dream Team?
Stop worrying about code quality and start scaling. [Contact XCEEDBD Today] for a free consultation on secure, high-performance IT outsourcing.
Frequently Asked Questions
Q1: What are the most common reasons outsourcing fails? Outsourcing typically fails due to poor communication, undefined project scope (scope creep), lack of detailed documentation, and treating the vendor as a “task doer” rather than a strategic partner.
Q2: How can I find a reliable outsourcing company? Look for reputation and reviews. Platforms like G2Crowd, Capterra, TrustRadius, or SoftwareAdvice allow you to read verified client reviews. Additionally, prioritize companies with a multinational presence and verifiable case studies.
Q3: Is outsourcing only about cutting costs? No. While cost reduction is a major benefit (often reducing administrative overhead and hourly rates), the primary drivers for modern businesses are access to specialized skills, faster time-to-market, and the ability to focus on core business functions.
Q4: Which countries are best for IT outsourcing? Avoid choosing solely based on the lowest price. Look for countries with strong educational infrastructure in technology and good English proficiency. India remains a top destination due to its vast talent pool, but Eastern Europe and Latin America are also strong contenders depending on your time zone requirements.
Q5: How do I protect my data when outsourcing? Use strict NDAs, require the use of VPNs (like ExpressVPN) for remote access, ensure the vendor follows ISO security standards, and mandate that your data be stored on segregated networks with limited access controls.




